Learn how to create OAuth credentialsclient_id, client_secret, and redirect URIs. They are a type of developer credential.

OAuth credentialsclient_id, client_secret, and redirect URIs. They are a type of developer credential.client and client parameters that are used to implement an OAuth 2.0
This tutorial shows you how to create OAuth credentials for use in app authentication and do the following:
- Configure privileges
Privileges are a set of permissions assigned to ArcGIS accounts, developer credentials, and applications that grant access to secure resources and functionality in ArcGIS. to allow your application to access ArcGIS services, content, and functionality. - Set authorized referrer URLs.
- Manage settings of the OAuth credentials and monitor usage using its item page
An item page is a web page in ArcGIS Online or the developer dashboard used to access and manage the properties for an item and the content it references such as a web map, hosted layer, or file. .
This tutorial focuses on creating OAuth 2.0 credentials for a private application with selected privileges and access.
Prerequisites
-
You need an ArcGIS Location Platform account
An ArcGIS Location Platform account, formerly known as an ArcGIS Developer account, is an identity associated with an ArcGIS Location Platform subscription. . -
You need to know the privileges
Privileges are a set of permissions assigned to ArcGIS accounts, developer credentials, and applications that grant access to secure resources and functionality in ArcGIS. required by your application. The privileges assigned to developer credentials allow your application to access ArcGIS services and resources.
Steps
Sign in to your portal
You use your portal to create and manage items, including OAuth credentials.
- In your web browser, go to https://location.arcgis.com, and sign in with your ArcGIS Location Platform account. In the dashboard, click My portal to go to your portal.
Create a new item
-
In your portal
ArcGIS portal, also known as a portal, is a website with applications and tools that can be used to create, manage, access, and share geospatial content and data. It supports security and authentication, developer credentials, content and data service management, user and group management, and site administration. A portal can be hosted in Esri's infrastructure or your own infrastructure. , click Content > My content > New item.

-
Click Developer credentials
Developer credentials are a type of item in a portal that contains parameters for authentication. There are two types of developer credentials: API key credentials and OAuth credentials. . -
In the credential type screen, select OAuth 2.0 credentials
OAuth credentials are an item that contains parameters required to implement user authentication or app authentication, including a and click Next.client_id,client_secret, and redirect URIs. They are a type of developer credential.
Need troubleshooting help?
If the Developer credentials option is not visible when creating a new item, your ArcGIS Online account does not have the correct permissions. You need an ArcGIS account with a user type of Creator or higher. Learn more about user types in the ArcGIS Online documentation.
If the Select credential type menu does not display when creating developer credentials, OAuth 2.0 credentials will still be created by default. This menu only displays if your account has privileges to create multiple types of developer credentials, such as API key credentials
Select application type
You can configure your OAuth 2.0 credentials in the Where will you use these credentials? menu to define how your credentials will be used. This setting restricts where and how the credentials can be used and helps prevent unauthorized access to secure services.
-
For this tutorial, select Private application with selected privileges and access.

-
Click Next.
Select items (optional)
If your application will require access to specific private items
-
If your token does not require item access, select No item access. Then, click Next.
-
Otherwise, select Grant access to specific items.
-
Select the items you want to grant access to. You can select up to 100 items in this menu.

-
Click Next.
Select privileges
You can configure the settings of OAuth 2.0 credentials to configure the privileges
-
In the Create developer credentials > Privileges window, browse the available privileges.

-
Browse the table below to view the available privileges, privilege strings, and descriptions for ArcGIS Location Platform:
-
Select the privileges required by your application and click Next.
Need troubleshooting help?
If the Privileges window is not visible when creating API key credentials, your ArcGIS Online account does not have the correct permissions. You need an ArcGIS account with a user type of Creator or higher. Your account must also have these additional privileges:
- General privileges > Content > Generate API keys
- General privileges > Content > Assign privileges to OAuth 2.0 applications
Your organization administrator can grant you these privileges using a custom role. To learn how, go to the ArcGIS Online documentation.
If you don't see a specific privilege in the Privileges window, there are several possible reasons:
- The application type you selected may only allow a limited set of privileges. To access a broader set of privileges, choose a different type of application in the Where will you use these credentials? menu.
- Certain location services are only available for ArcGIS Location Platform. Check the privileges available for your product type in Security and authentication > Privileges.
- If you have an ArcGIS Location Platform account, you need to enable pay-as-you-go
Pay-as-you-go refers to a type of billing where services are metered and you pay only for the services you use. in the Billing section of your dashboard to access some services, such as the GeoEnrichment service. - If you have an ArcGIS Online account, your account may not have the correct role to access the services you need. Contact your organization administrator.
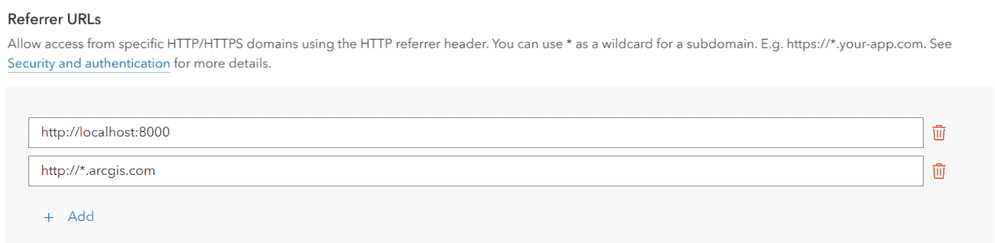
Set referrer URLs
You can set referrer URLs on OAuth credentialsclient_id, client_secret, and redirect URIs. They are a type of developer credential.
-
In the next window, scroll down to Referrer URLs.
-
Set the Referrers field to the web domains you would like to restrict the access token to. To learn more about referrers, go to OAuth credentials (for app authentication).
-
Click Next.
Save the item
After configuring the properties of your OAuth credentials, you can save the credentials as a new item
-
In the Create developer credentials window, set the following properties:
- Title:
My OAuth credentials (for app authentication) - Folder:
Developer credentials(Create a new folder) - Tags: Add tags related to the privileges
Privileges are a set of permissions assigned to ArcGIS accounts, developer credentials, and applications that grant access to secure resources and functionality in ArcGIS. of the credentials. - Description: Describe the application that these developer credentials will be used in.

Click Next.
- Title:
-
In the Summary window, review the properties, privileges
Privileges are a set of permissions assigned to ArcGIS accounts, developer credentials, and applications that grant access to secure resources and functionality in ArcGIS. , and item access you have set. -
Click Create to create your OAuth credentials
OAuth credentials are an item that contains parameters required to implement user authentication or app authentication, including a .client_id,client_secret, and redirect URIs. They are a type of developer credential.
Copy the client ID and client secret
Your OAuth credentialsclient_id, client_secret, and redirect URIs. They are a type of developer credential.client and client parameters that are required to implement app authentication
-
On the item page
An item page is a web page in ArcGIS Online or the developer dashboard used to access and manage the properties for an item and the content it references such as a web map, hosted layer, or file. of your OAuth credentials, scroll down to Credentials. -
Copy the Client ID and Client Secret values and paste them into your application. Never expose the value of your client secret.

Manage your credentials
After creating an OAuth credentialsclient_id, client_secret, and redirect URIs. They are a type of developer credential.
To learn more and see management steps, go to OAuth credentials (for app authentication).
Additional resources
Learn more about app authentication