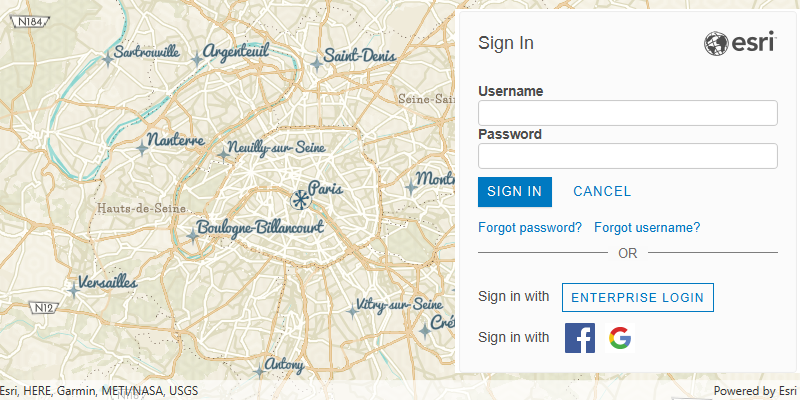
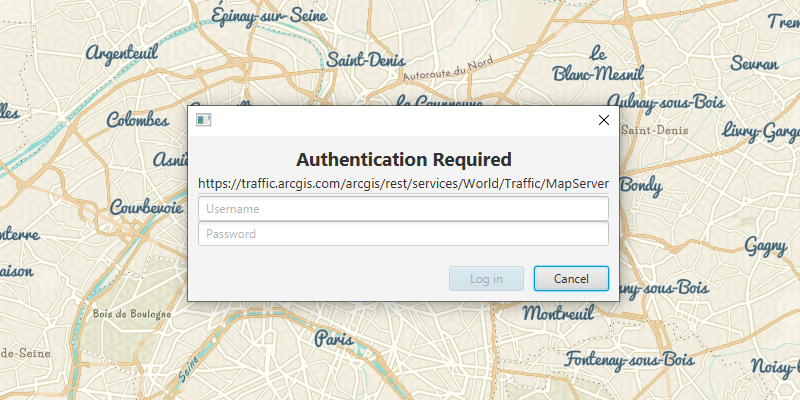
ArcGIS supports secure access to ArcGIS services and portal items. It ensures that only valid, authorized users and services can access protected information. To access secure ArcGIS resources, you need an access token that you can obtain by implementing an authentication workflow in your app. The type of authentication you use depends on the security and access requirements of your app.
Learn more about authentication in the following topics:
- Types of authentication—describes the available types of authentication and offers help choosing the right one for your app.
- Types of credentials—lists the available credential types and describes how they're used.
- Implement authentication—provides guidance for implementing authentication in your app using the Authentication toolkit component or the Authentication API.